Today, with the effect of the coronavirus, the entire world’s dependence on the Internet and data has naturally increased, also an indispensable blessing for hackers been nature. So much so that while the epidemic killed thousands of people every day, hackers crashed the systems of even hospitals in several countries, capturing data and demanding ransoms.
In addition, there is a large increase in cyber attacks on social media platforms and all kinds of services that we use as end users. Well, how do you know if you have been affected by the attacks that have happened so far and are said to have affected millions of people? Here’s a platform that helps us do this: Am I bullied?
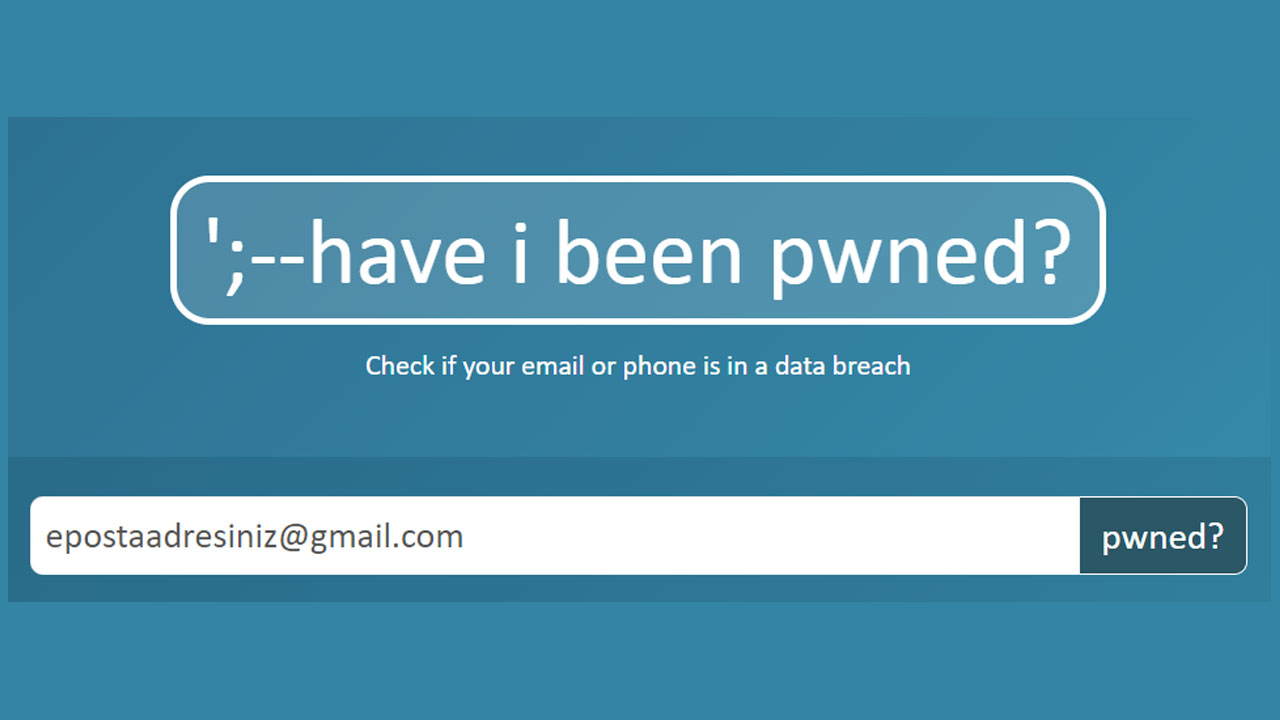
What is Have I Been Pwned?
Australian Regional Manager and winner of Microsoft’s Most Valuable Professional award Founded by Troy Hunt With Have I Been Pwned you can find out if your email, phone number or password has been hacked by others. The platform interrogates the email you request with the emails appearing in data breaches and Which data was hacked in which data breach? shows.
How do I use Have I Been Pwned?
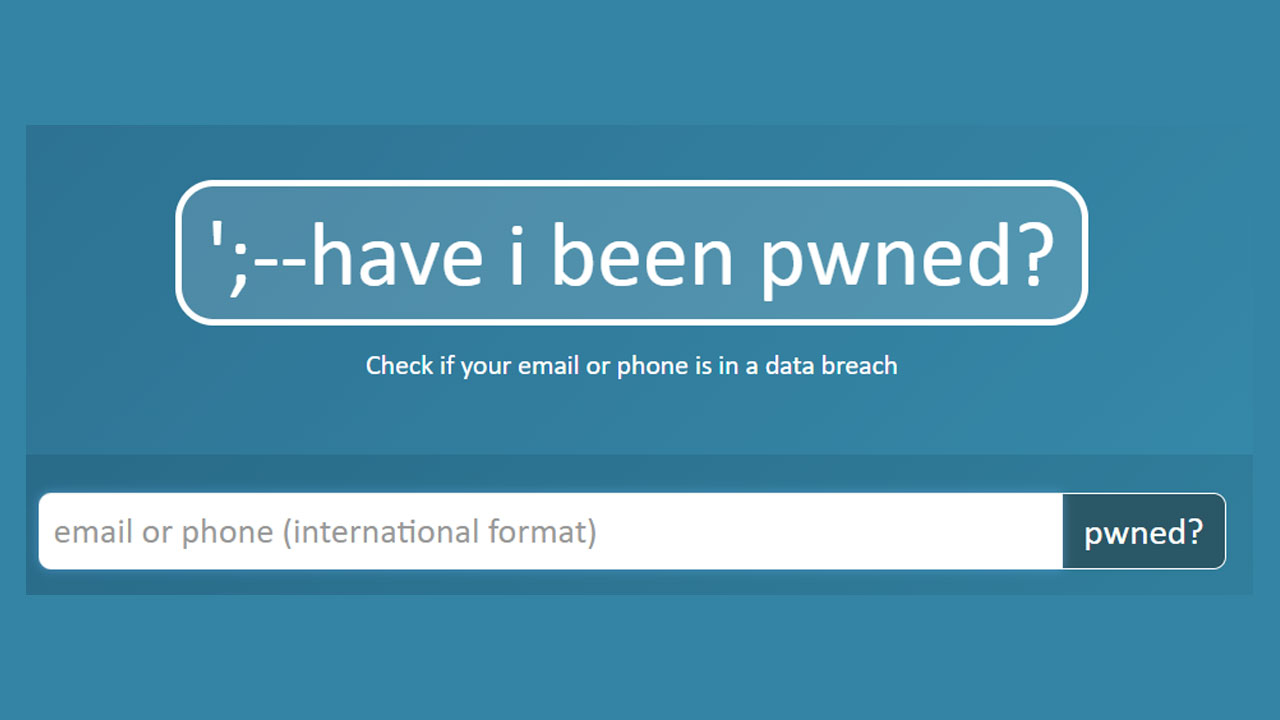
Using Have I Been Pwned is quite simple. If you are wondering if your information has been previously exposed to a data breach, you can find out by following the steps below:
- Step 1: Click here to go to Have I Been Pwned.
- Step 2: to the box your email address or phone number during the summer.
- Step 3: ‘pinned?Click the ‘ button and find out which of your data has been hacked.
- Step #4: The Password You Use Click here to find out if it has been compromised in any way.
- Step #5: Enter the password you want to request in the box.
- Step #6: ‘teased?’ Click the button to find out if your password has been hacked before.
Step 1: Click here to go to Have I Been Pwned.
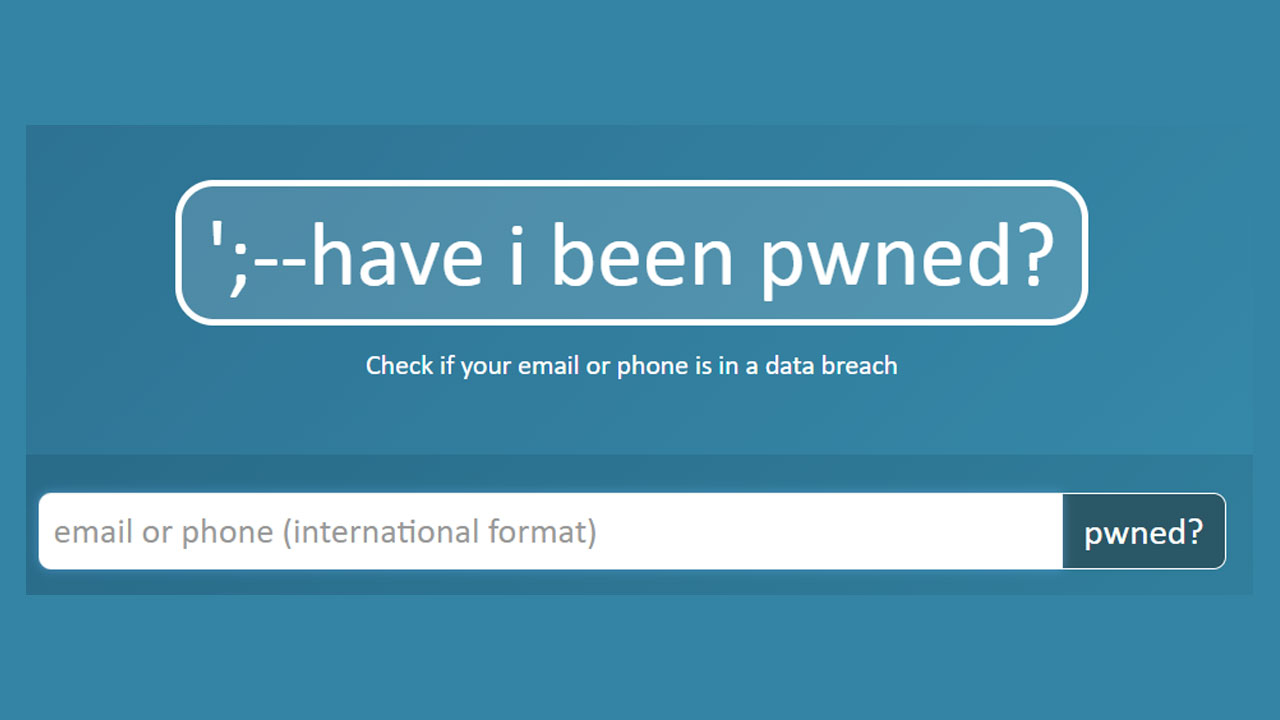
Step 2: Write your email address or phone number in the box.
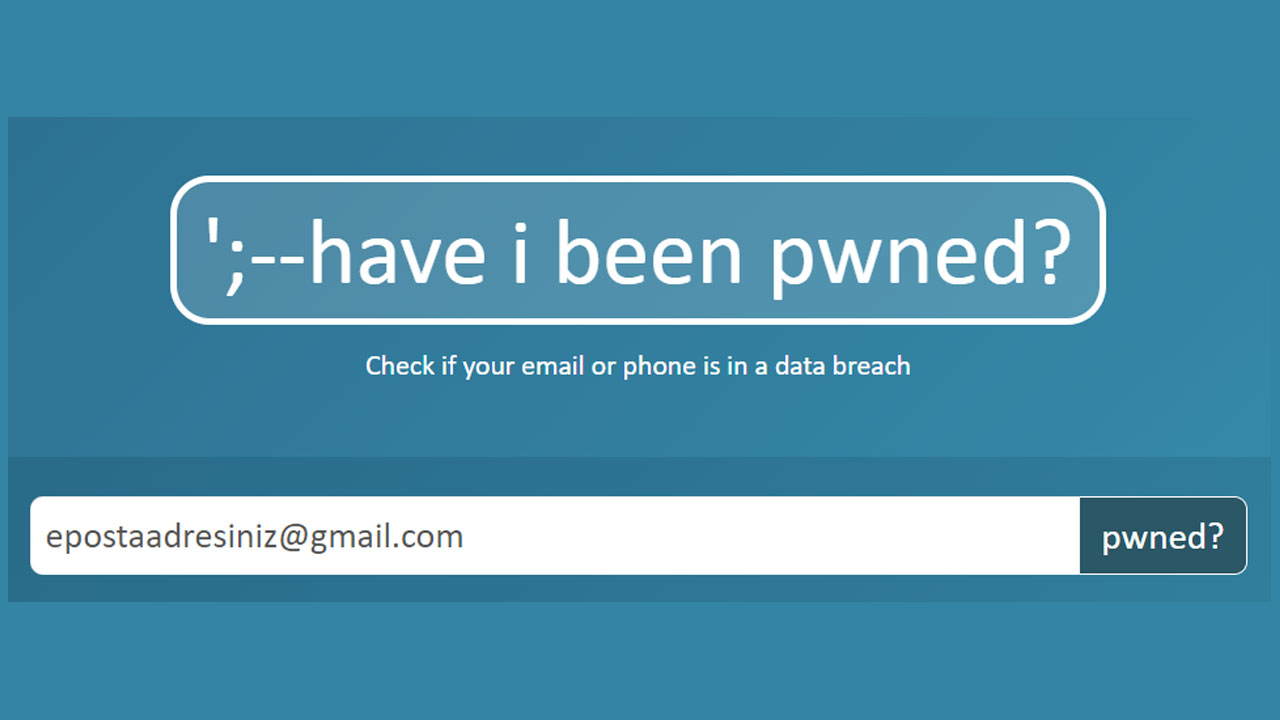
After opening the website, click on the box in front of you. your email or phone number during the summer.
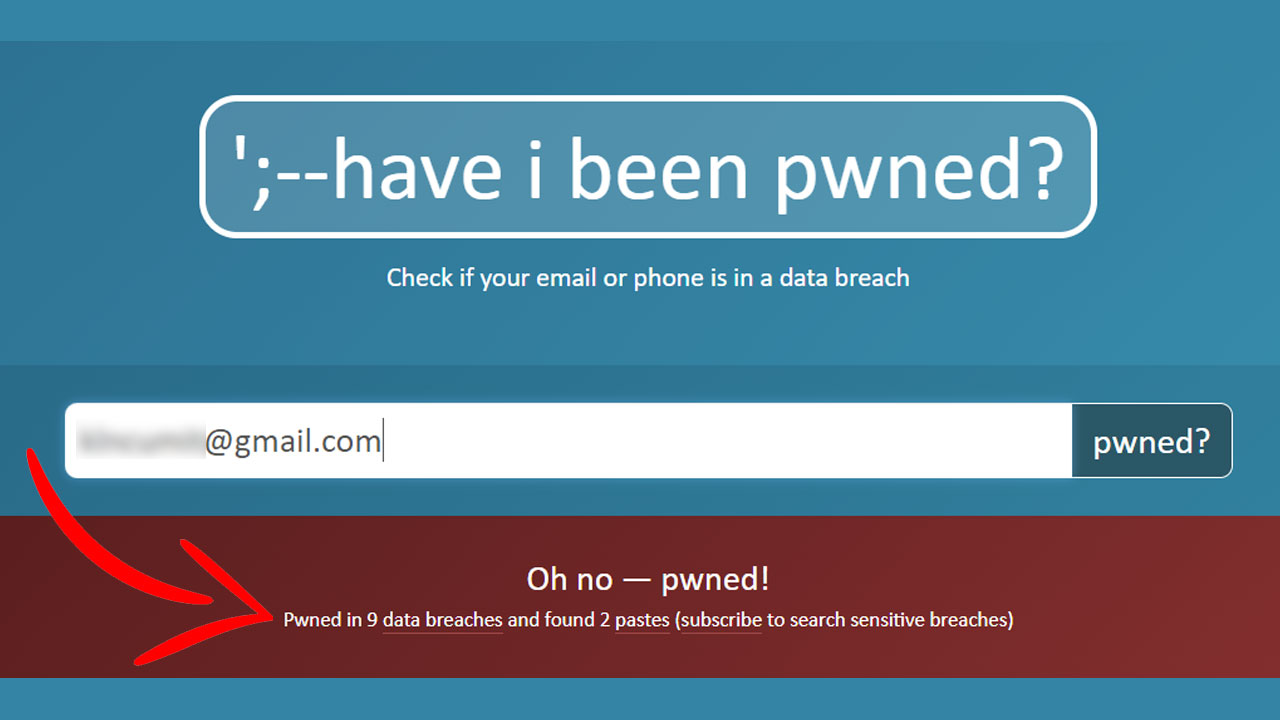
Step #3: ‘pwd?’ Click the button and find out which of your information has been compromised.
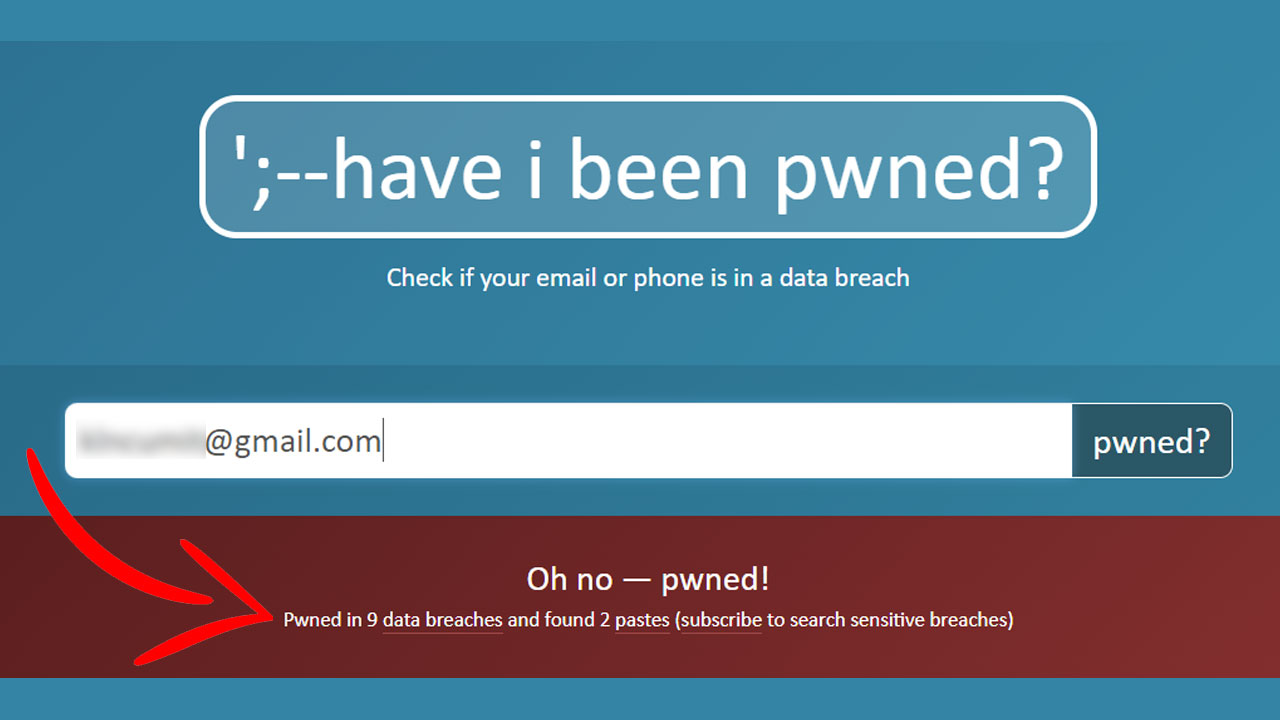
After entering the information you want to request’pinned?Press the button. The site scans the database and shows you in which data breaches the information you entered has appeared before. If the background color of the site is red, you may need to take action and change your information. If it’s green, it means none of your data has been captured (According to the information in the database). You can also see how many leaks your email address or phone number has appeared in from the place you see in the image.
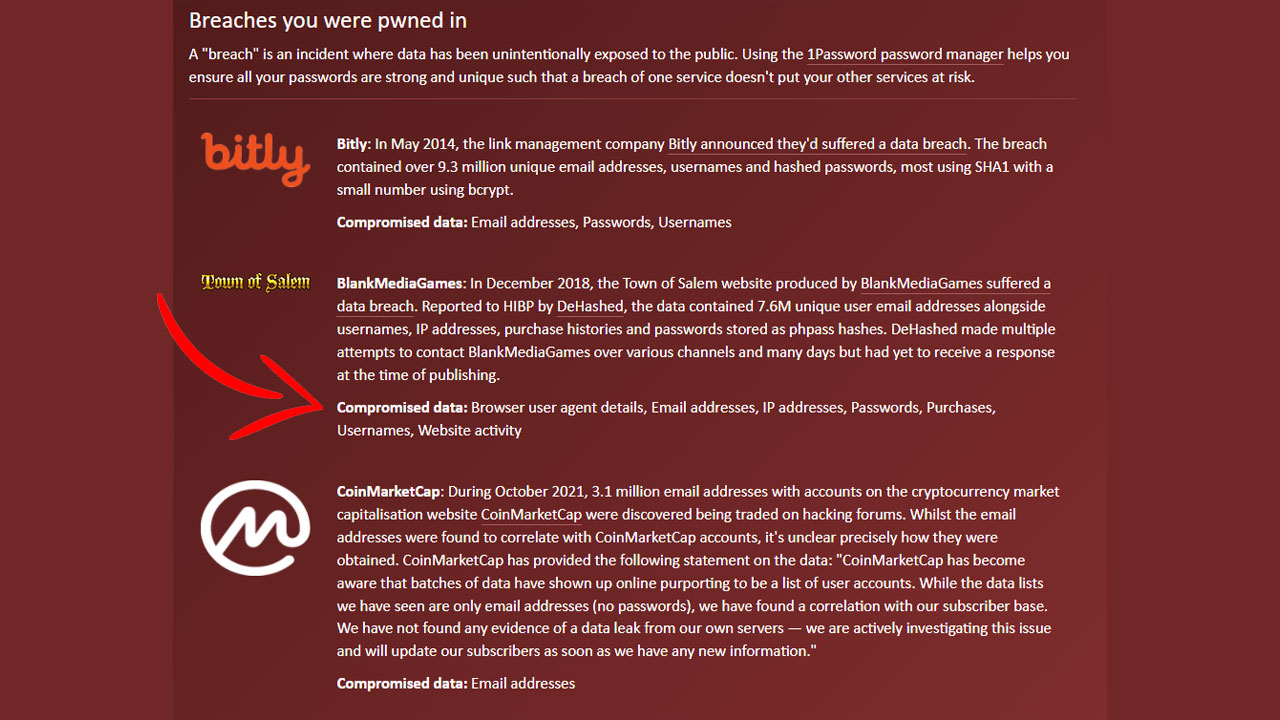
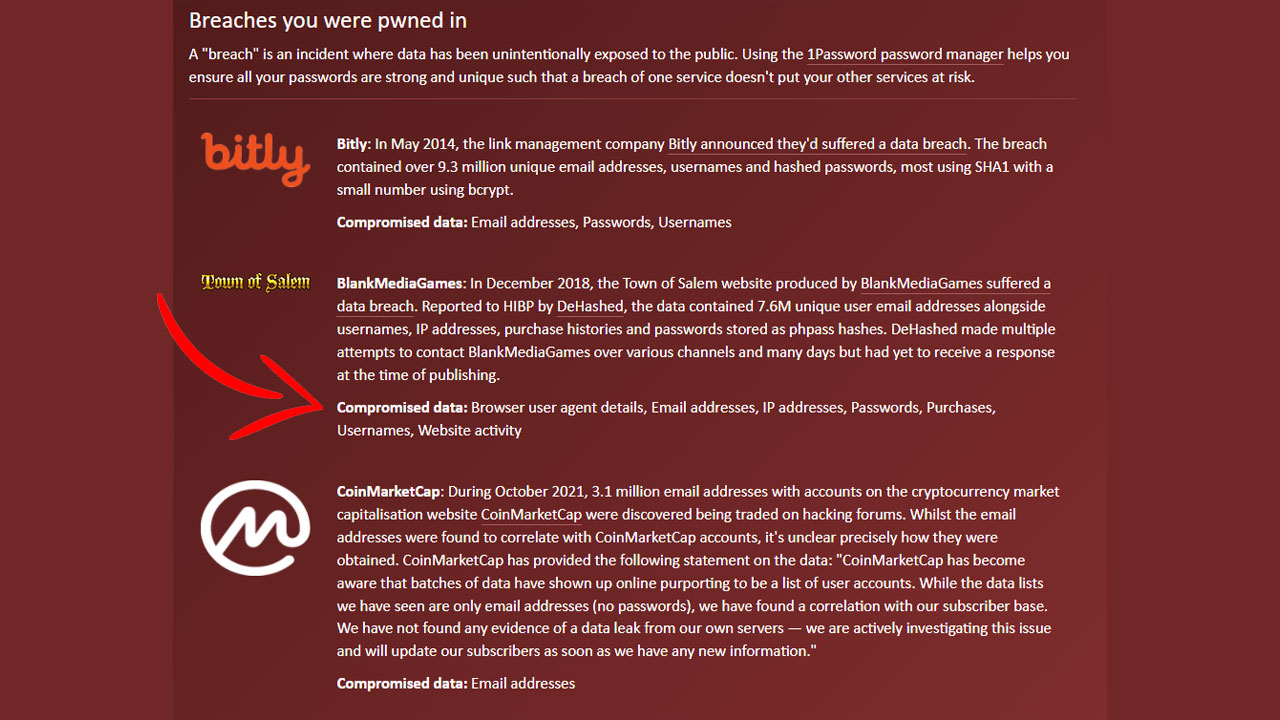
You can also see where your information is coming from one by one by scrolling down. Based on the information you have entered here, the data that matches you in the requested database and your other recorded information related to this data will also be listed. For example, the image above mentions that 7.6 million users were contacted on BlankMediaGames in December 2018. Along with the email address I requested in the ‘Compromised data’ section Details of my IP address, password, purchase history, username and website activity We can see it has been captured.
- REMARK: Not every data breach in the world is stored on the website. Therefore, you may not be able to get information about current data breaches like Yemeksepeti.
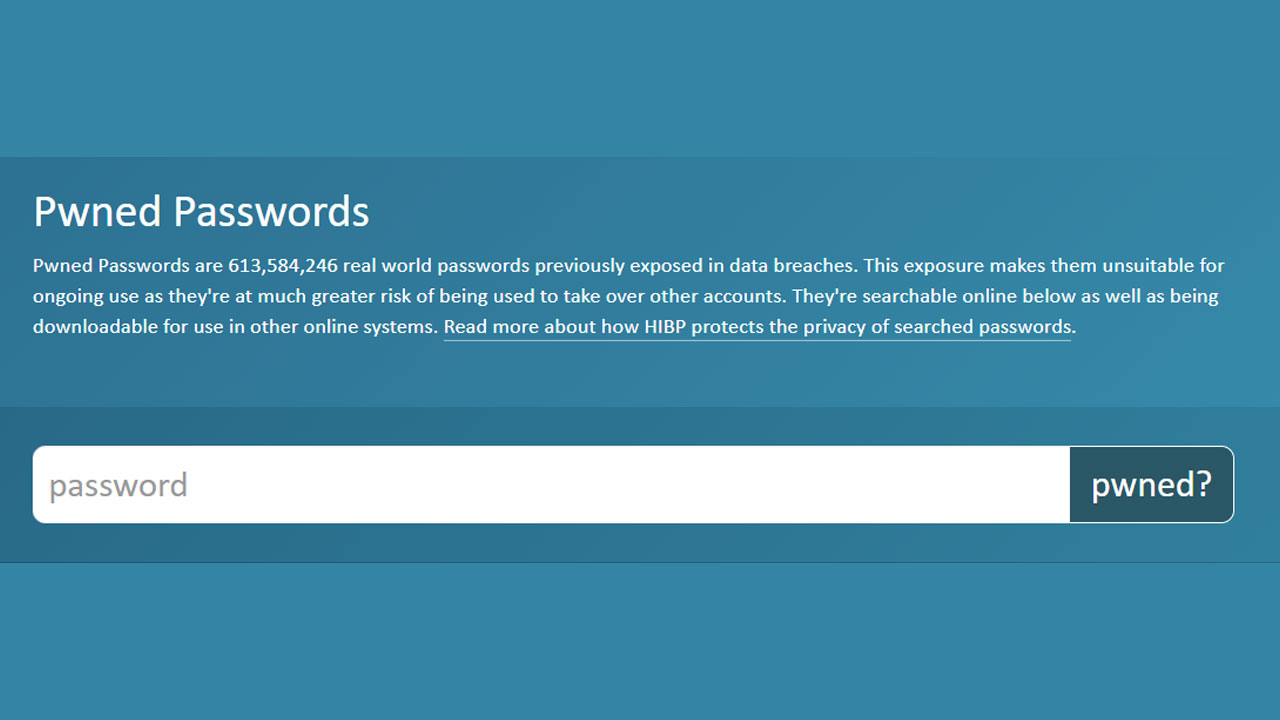
Step 4: Click here to find out if your password has been hacked in any way.
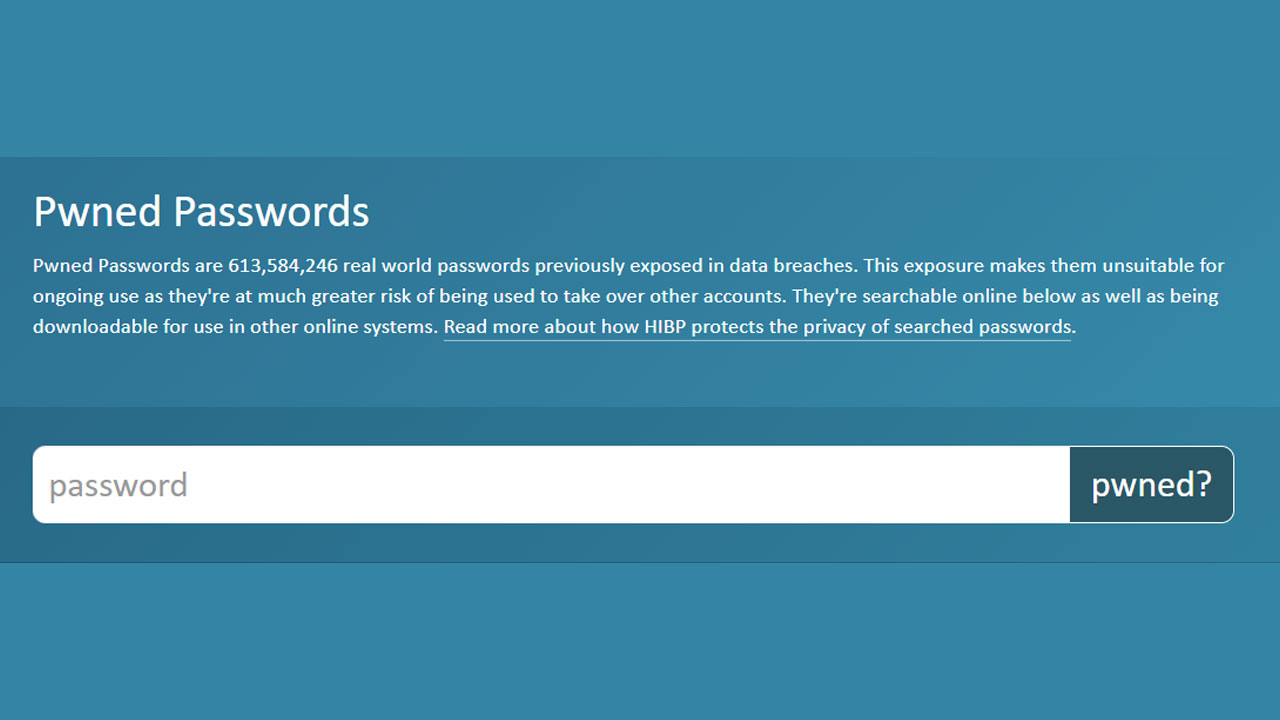
Am I Pwd? whether passwords are also compromised It makes it easy to ask. To ask this question: to this link click to go to the relevant page of the website.
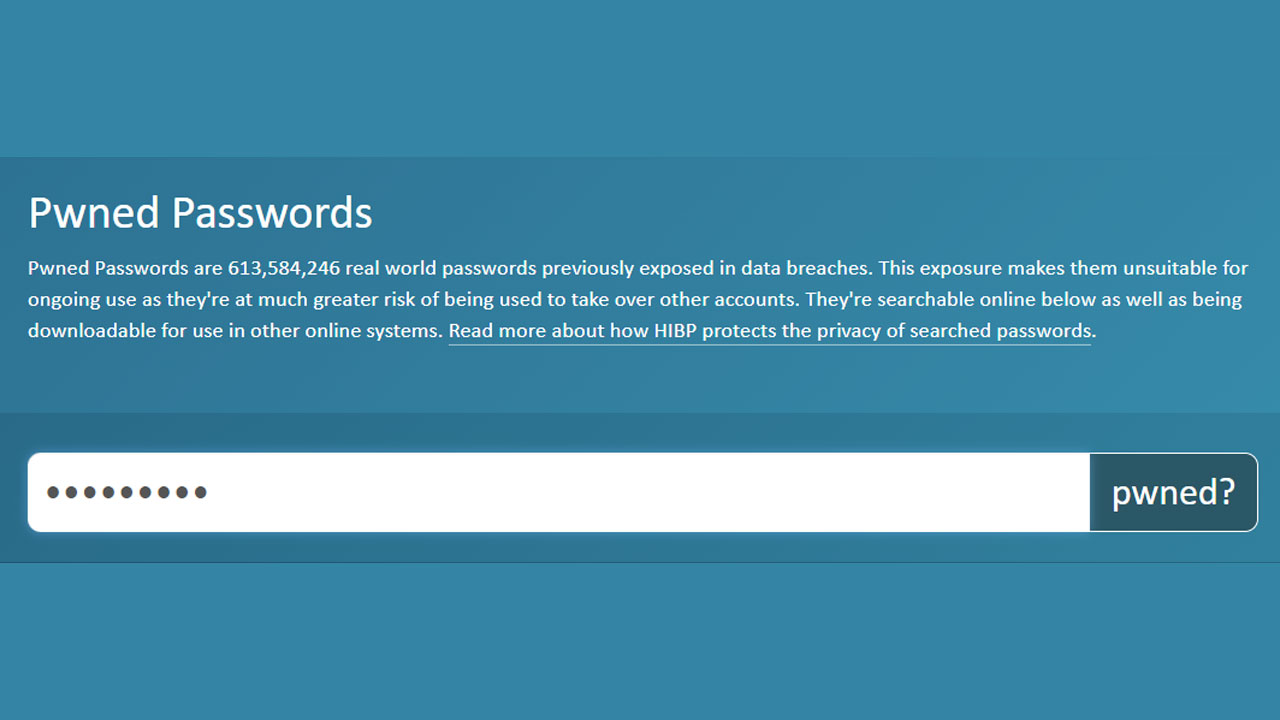
Step #5: Enter the password you want to request in the box.
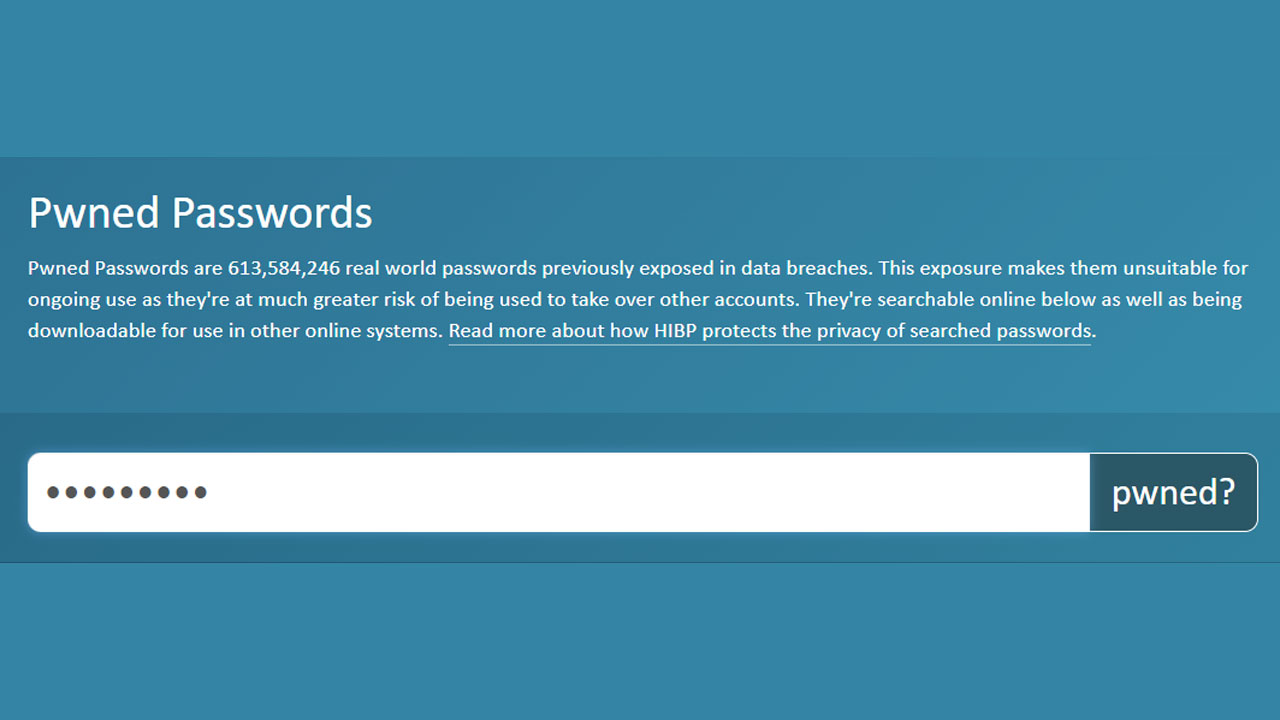
Just like you request your e-mail address and phone number, you can enter the password you want to request here. type in the box.
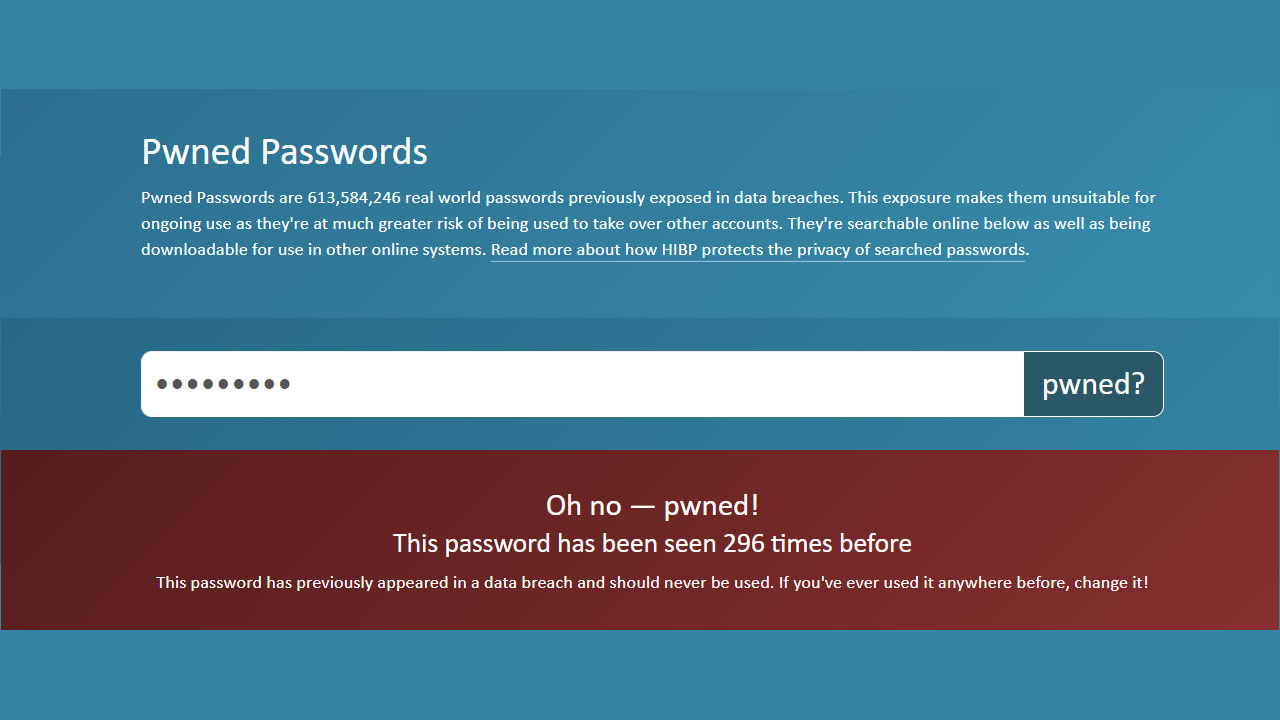
Step #6: ‘pwd?’ Click the button to find out if your password has been hacked before.
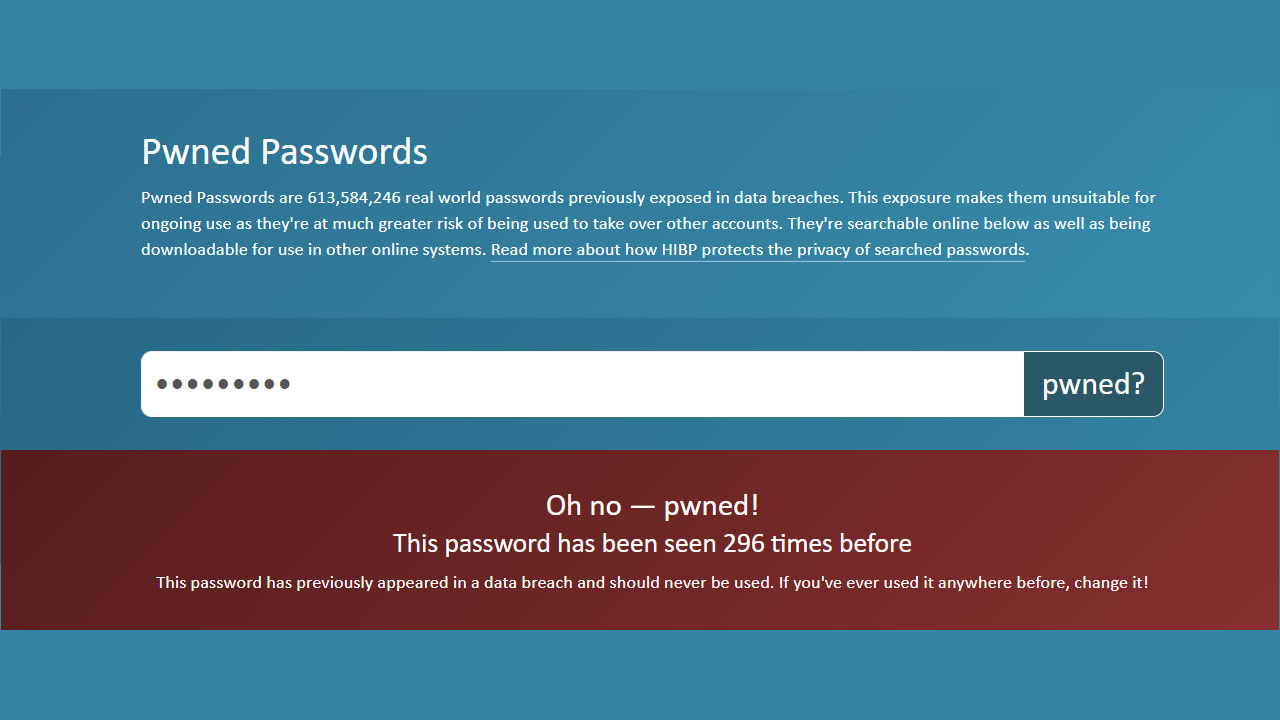
“Teased?” Click the button and look at the result. If you managed to keep your password strong enough, the page will turn green. But if you haven’t kept your password strong and used it over and over, the page will turn red and It has been seen hundreds of times in different places. you will see.
If you see that your password has been compromised, it is in your best interest to change your accounts password to a secure and complex one as soon as possible. How to make a strong password If you want to know, you can check out our article below:
Well, we questioned our email address, password and phone number on the site. Is Have I Been Pwned Reliable?

Troy Hunt, the founder and administrator of the website, has asked this question before. When you search for your email on the website, the email is only taken on a journey to find a matching email in a database stored in a Windows Azure storage. If there is matching information in any of the data breaches, the results will be displayed. The information you are looking for is not recorded in any way.
On the other hand, it cannot be said that the website is absolutely secure. Troy Hunt,How do I know if the website is hiding emails somewhere?In answer to the question “You don’t know, but he doesn’t hide it.he replied. Although he promises that he does not store emails in any way, he is still talking about trust. if you are in doubt, You may not use the website stated. He also indicates that this applies to every website. While Troy Hunt has become more credible in terms of security, we also recommend that you do not use this website if you are in any doubt.
- Turkey entered into a partnership with Have I Been Pwned on August 9, 2021. Thus it became the 26th government to collaborate with Have I Been Pwned.
How can you keep yourself safe?

It is very difficult to be safe on the internet. Even the platforms you trust most can be exposed to cyber-attacks from time to time and the information can be captured there. Even the websites you visit, the files you download, the emails you read can lead to all your information being made public. So it’s impossible to keep yourself safe, but you can follow these methods to better protect your information:
- Unknown, suspicious-looking and apparently suspicious emails Definitely don’t open.
- your devices in the latest version Pay attention that.
- Complex with upper and lower case letters, numbers and special characters strong passwords make and use.
- Two-factor authentication method Use it on every possible platform.
- you are going to visit addresses of websites Check it out, stay away from suspicious addresses.
- The address of the website in the address bar If it doesn’t start with “https://” Do not give your information to these websites.
- When downloading a file against suspicious downloads aware.
Even if you do all this and more, your information that you can never fully protect to remind.